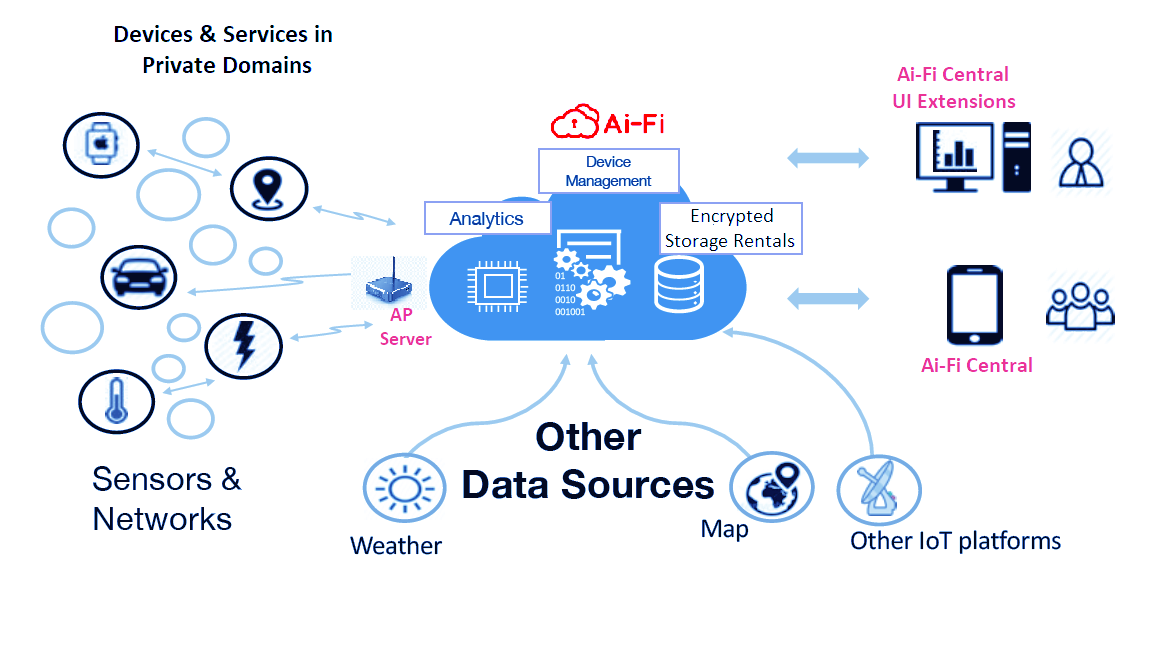
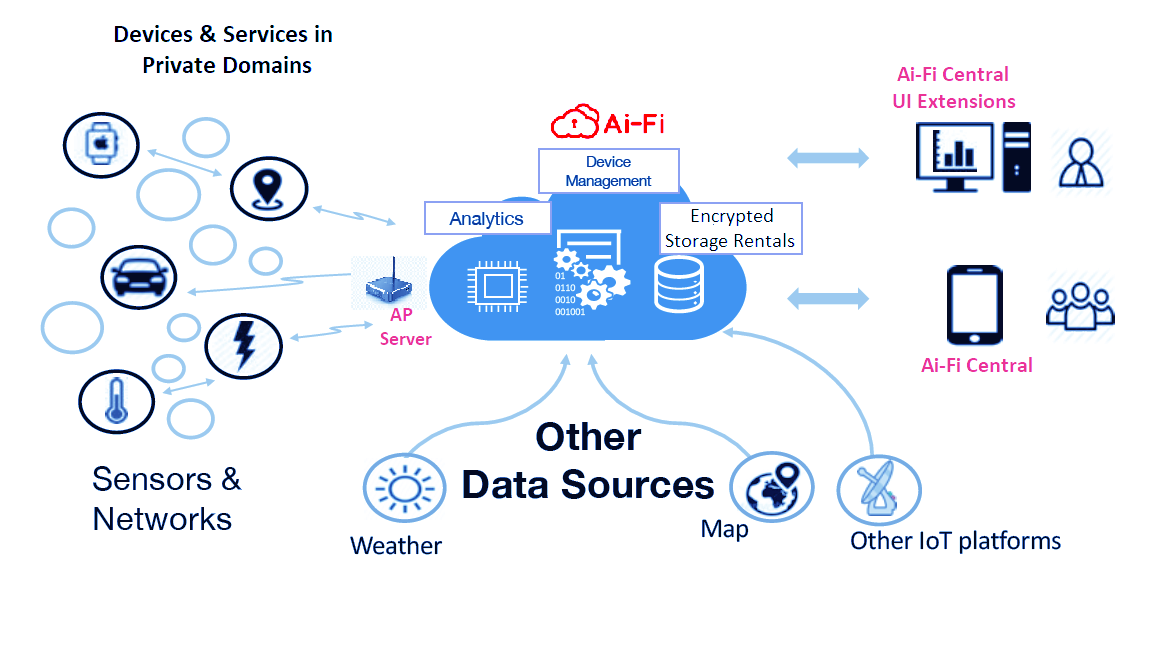
Ai-Fi Architecture
In this page we will describe those architectural components that the Ai-Fi infrastructure is based on. Their
implementation and deliveries are to follow a phased plan, which will be further detailed out in our
Roadmap.
In a nutshell, Ai-Fi is your best friend in commanding and controlling your various
devices, either locally or remotely, through the most private and secured
Ai-Fi infrastructure. All access are carried out through the client app,
the "Ai-Fi Central", which runs on your mobile phones with a inbuilt crypto
Ai-Fi Wallet for managing your many DiDs (Decentralized Identifiers).
Under Ai-Fi, access to
remote resources such as your smart devices at home is protected and
conducted within the confinement of a private "Domain", which is to be
gated by an "Home Server" that functions as a firewall. For
private and secured access to remote gated resources, the Ai-Fi Service Cloud
provides the most transparent, non-tracking, and warrant-proof connectivity. To
remove the possible interference by Ai-Fi.net and other hacking attempts, this infrastructure further
adopts the blockchain technologies to provide the necessary transparency to counter-balance
any men in the middle. All encryption keys are negotiated end-to-end directly between Ai-Fi Centrals
or between an Ai-Fi Central to Home Servers. Ai-Fi in the middle has no visibility
into the traffic and is incapable of collecting metadata between the corresponding parties.
Ai-Fi Central is an app which is to run on your mobile phone. The installation is
fairly straightforward: select the appropriate package for your platform,
download from the App Store, and run with it. With Ai-Fi Central alone you can have fun already
in taking secure notes, keeping track of your passwords, and sending/receiving
secure emails. For extending the fun to your other network assets, including
the saving of your encrypted emails, backing up your photos from your mobile
phone, remotely control your smart devices at home, and
distributing multiple copies of your files to many remote devices
or sites, you need to first fence in those remote devices in one or multiple
Ai-Fi Domains in order to protect them from encroachment by
bad elements roaming around the Internet. Each of those domains must be gated by
an Ai-Fi Home Server
as previously mentioned.
Setting up the Home Server is a bit more involved. The
most straightforward approach is to acquire a ready-made server
box
directly from our Amazon store with software pre-installed.
For those technically
endowed, you don't need to buy from Amazon. You just need to install the
Ai-Fi Home Server software on a Linux server box, or install the software to a
Docker container. The Raspberry Pi 4 is a popular choice among some of our users.
We are a totally open-sourced operation and you can
download or even build your own Ai-Fi Home server
from our Github site.
Once the server software is appropriately installed on a Linux server or container, you are
good to go by following the deployment instructions.
With the advent of IoT and the desire to protect your privacy and personal data, as
a citizen of the Internet, you do need to have the readiness or willingness
to learn about how to protect yourself from hackers and bad actors under
the current surveillance capitalism. We can only prepare you so much with
our infrastructure. However, worry you not: we have made the installation of
your Home Server as easy as that for any of your IoT gadgets.
As of V. 2.0, the installation package is only available for Raspberry Pi 4.
Application Transparency
Ai-Fi.net offers a complete IPv4 address space for your private network or Intranet, which liberates your LAN-challenged
applications from their parochial confinement. Gone is the dependency on the cloud for Intranet connectivity and
its unintended implication on your privacy.
For conventional applications, which usually require addressability among their components and are therefore
typically restricted to a confined LAN, Ai-Fi.net is able to extend their network coverage to all corners of the world via
an Ai-Fi configuration of multiple branches.
Traditionally, to extend network applications beyond their immediate environment, some kind of
public addressability is required. Nowadays this is usually done via the cloud, namely finding a centrally located
cloud service with public IP addresses so all other devices may interconnect through this central cloud
in a star configuration. Along the way one loses the physical possession of those critical servers consigned to a
third-party cloud and the precious privacy afforded only by physically owning one's devices.
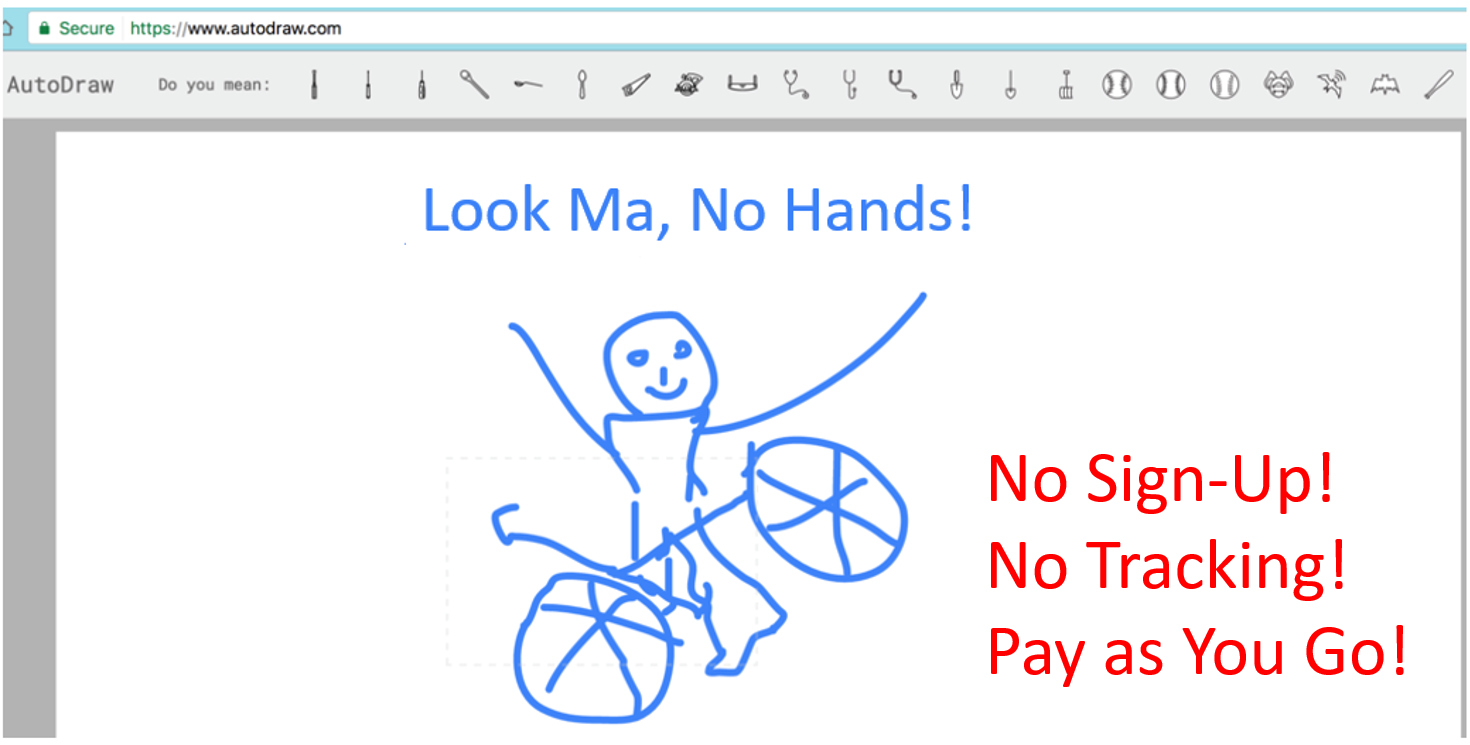
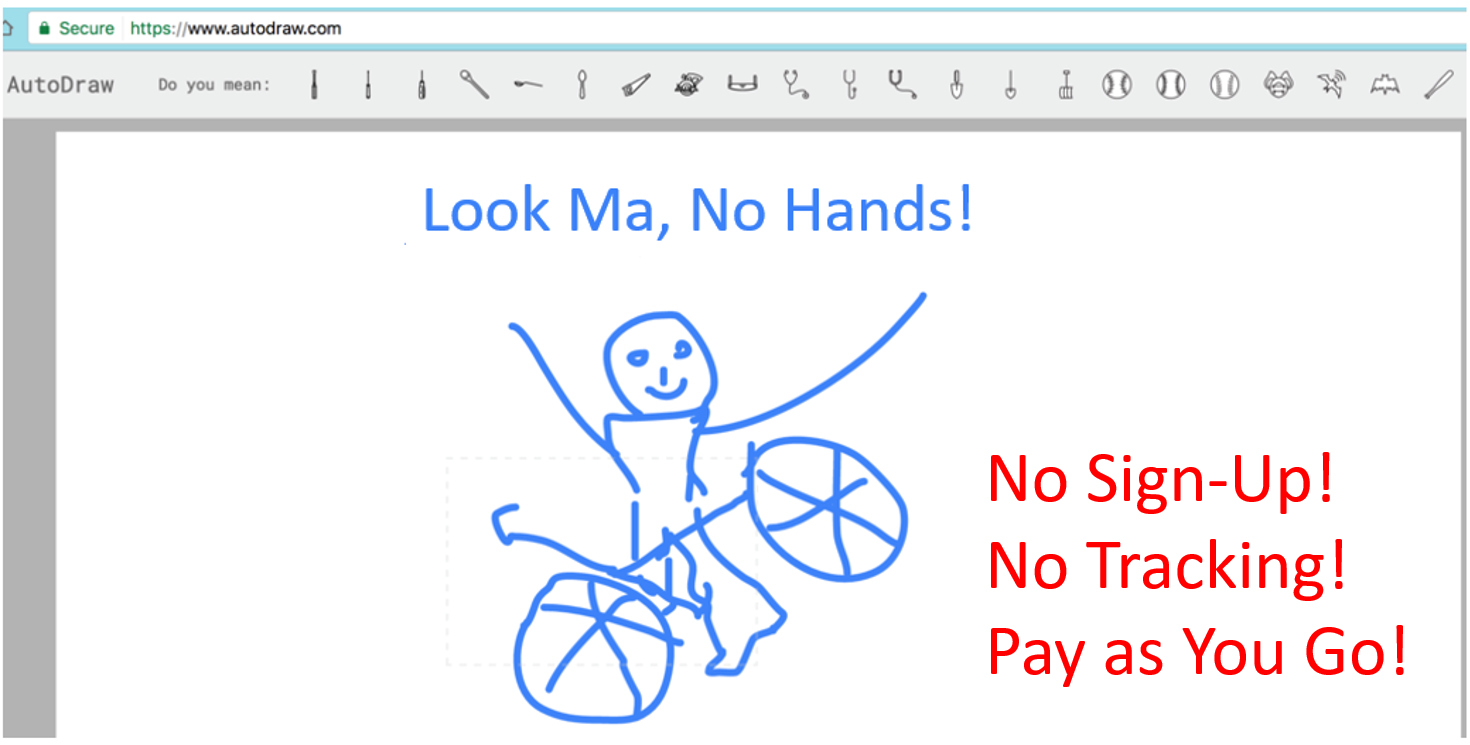
No Sign-up Procedure
First and foremost, Ai-Fi.net is a non-tracking shared resources for helping Ai-Fi users manage their
private networks, or "Domains"
as they are called, and protect their access to or from the public Internet. It is designed to
maximize their privacy while allowing the construction of an exclusive range of networks for themselves, their
families, and their communities. In its core an entirely new design principle of DiD (Decentralized Identifier) and
Decentralized Pubic Key Infrastructure (DPKI) are followed. The singular characteristics of this DiD based
identity management design conducted through a blockchain-based Ai-Fi Wallet is the large number of "identities"
implemented per the involved application scenarios according to the "Privacy by Design" principle.
Consequently, to participate
in the Ai-Fi ecosystem there is no sign-up required. Authentication and authorization are conducted
by the Ai-Fi users directly without needing any third-party proxies. However, this eradication of
"free services" illusion implies that our users have to carry the cost of running the Ai-Fi
infrastructure collectively (and anonymously), which is kept at a very reasonable rate.
Our members carry out their Ai-Fi operations pseudonymously based on the same
account protection design as in Bitcoin.
Their personal or community domains are segregated from each other but still allowing supervised
inter-domain access and firewall protections.
Although Ai-Fi.net may be deployed in 5 steps or less, it is much more than a single App. Its function set is
delivered through the following apps:
- Ai-Fi Cloud Access: This is also known as the Wallet App. It creates your Ai-Fi wallet and the domain-wide CFG (configuration file) for your
branches and other access control rules. It only runs on Apple or Android phones, with limited extensions to Windows and Apple Mac.
- AP (Access Point) App: This is the App for controlling the ingress/egress of a branch. It may run on dedicated
hardware like a Raspberry Pi based controller, or PCs running Microsoft Windows or Apple Macs.
- RA (Remote Access) App: This allows domain members to access various private branches from the Internet.
These Apps are to be installed to various architectural elements in Ai-Fi.net according to their intended functions:
- Ai-Fi AP (Access Point) Management: This administers how our members are referenced through various applications with them
in exclusive control over their credentials.
- Domain and Branch Configuration, Access, and Control: This is how your private networks are configured
and managed through the AP (Access Point) App. The configuration is centrally administered in a multi-tenant SaaS
fashion. The branches may be distributed across the Internet.
- Internet Access Control: This is the support for incoming/outgoing traffic from/to the Internet. These external
visits can be made either through the Ai-Fi HomeCloud App or directly as a public access with the Home Server as
the firewall.
Pseudonymity
When first participating, an Ai-Fi user creates their own wallet in order to manage many different
accounts utilized as identifiers under various application contexts. Once created, all
Ai-Fi functions are carried out pseudonymously, identifiable only through their assigned crypto accounts
in the wallet relative to their respective application context without being directly associated with any
other of the owner's worldly identities such as
their cell phones, email addresses, SSN, or credit cards. In other words, the Ai-Fi Wallet maintains a large number
of crypto accounts to protect their self administered DiDs (Decentralized Identifiers), which are individually
managed and applied per associated applications. Those DiDs are further managed through
the Ai-Fi Digital Asset Framework.
The Wallet App safeguards your many account credentials and the domain-wide CFG (configuration file).
The deployment of your domains
is based on this CFG you've defined, after that
you enable one by one individual Home Servers for various branches.
Account-less and Decentralized
There is no need to sign up for an account in order to participate in the Ai-Fi ecosystem. Instead,
an Ai-Fi member is expected to create and own their individual Ai-Fi wallet on their mobile phones
where it is physically/exclusively hosted and managed from. This
is to eliminate any possibilities of tracking but still to be able to pay for various Ai-Fi security services. There is no free
lunch, contrary to what those "free" services lead you to believe, but Ai-Fi charges very reasonably.
An Ai-Fi account is protected by two independent verification factors:
- Your mobile phone where your Ai-Fi Wallet is created on
- The Ai-Fi Central application PIN, also local to your phone
The Wallet App installed on your phones with its wallet and private CFG is
depicted on the bottom right of the below diagram:
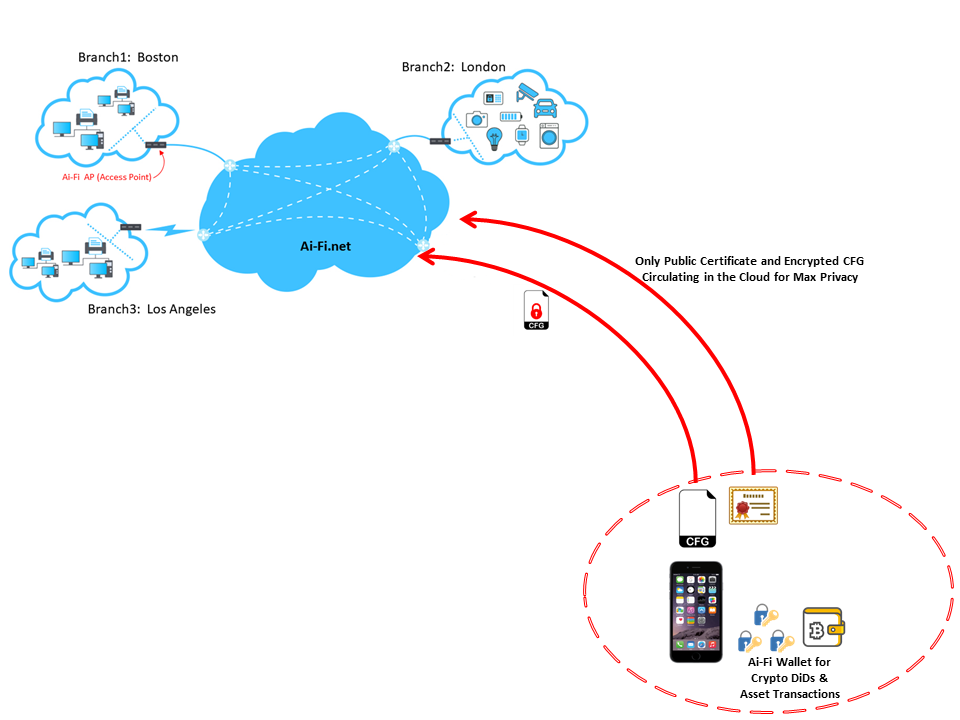
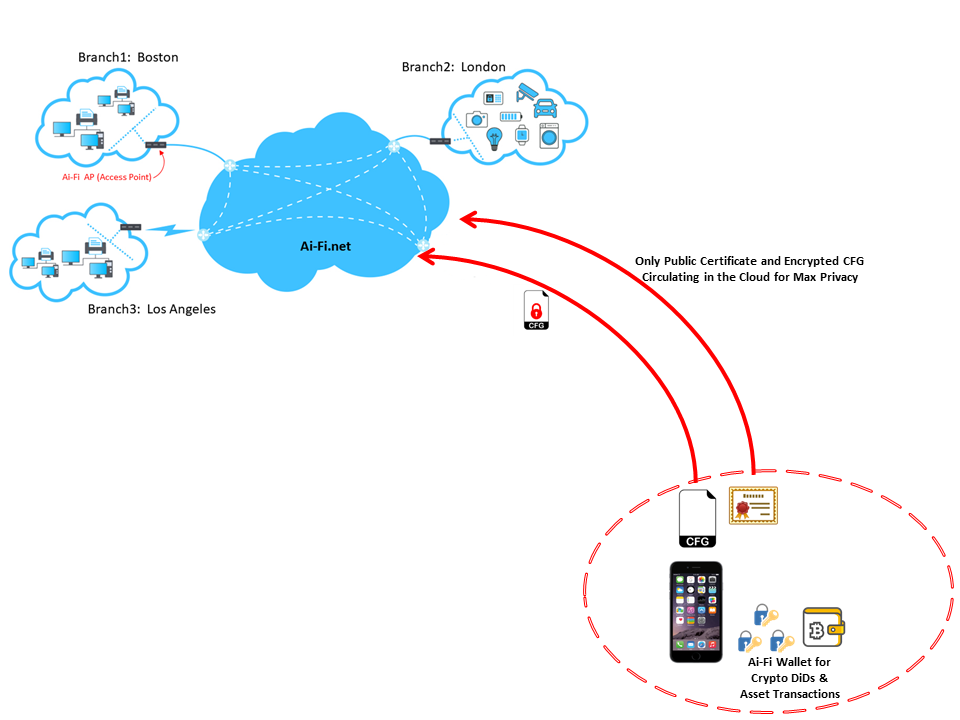
In addition to storing members' credentials in their personal phones, during the Ai-Fi operations for delivering Secure Email or other functions that may require email address or payment, the technology of AnonymousCloud is further adopted to enforce the Ai-Fi pseudonymity requirement so that our members are not traceable beyond their pseudonymous accounts. For details, please look into our blog on Security.
Global Configuration
Domain Configuration
The goal of the Ai-Fi Domain is to allow all devices to be distributed over a wide area but still able to work together as if they were sharing an unrestricted LAN. A domain is further afforded a complete set of IPv4 addresses so it can be managed with ample flexibility in terms of address plan. Design your domain layout before installing any software.
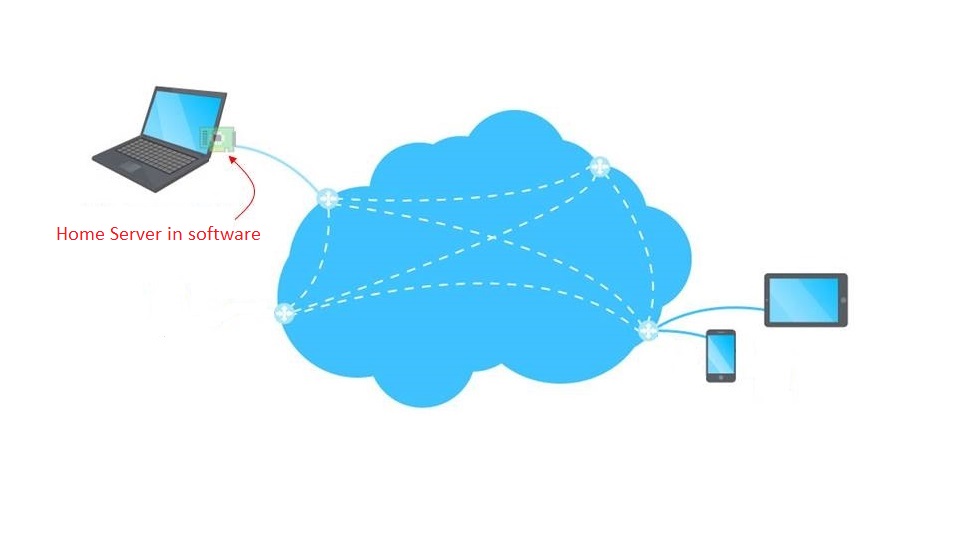
Minimal Configuration
(Useful Test Scenario)
Download the Ai-Fi Central app onto your smart phone and create a private wallet through the app. Use the
same app to define your only branch consisting of a single PC.
Next install the appropriate Home Server package software onto
your Windows PC or Apple Mac so it can be remotely accessed by your smart phone. You may turn it
into a public web server or other home servers even while you have no public IP addresses.
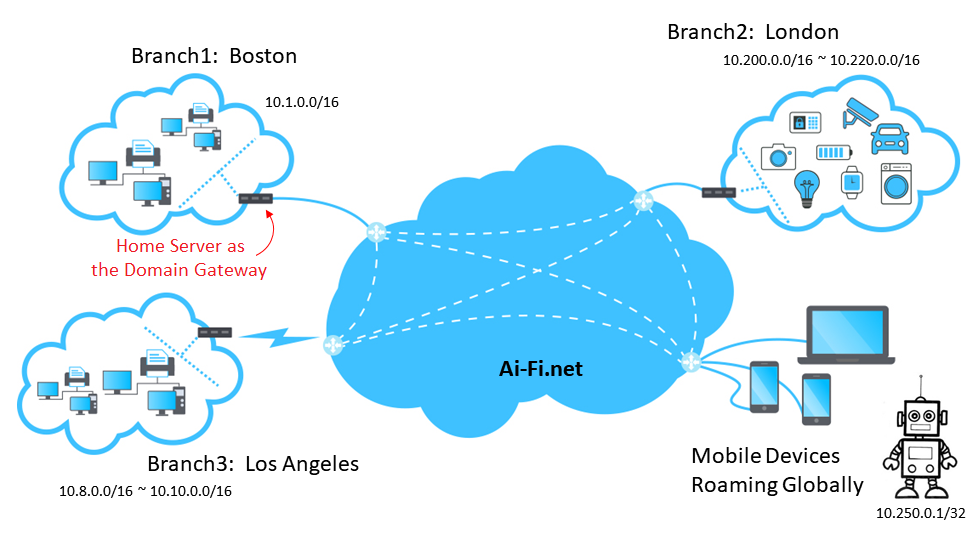
Multi-Branch Configuration
Install the Account App to
your smart phone and define the domain database to include all branches to be deployed as in
the Minimal Configuration. Move on individually to your PC, Mac or
other Linux appliances such as Raspberry Pi to create Home Servers by installing
the appropriate Home Server software, one for each of
your branch, typically situated apart from other branches. All branches within the same domain may
freely address each other as if they are all located in the same LAN.
For the upper right London Branch with all the IoT devices depicted, those "things" may spread out
geographically, for which you need to follow the instruction for IoT deployment.
If you have some highly mobile devices such as the robot on the left,
it may be defined as a self-contained branch (with only a single device included) in order to allow for its high roaming requirement.
Integrated IoT Home Kits Bridges
The advances of IoT inject smart into things all around us, which will not fulfill
their potentials unless they can be controlled from anywhere at anytime. This vision of
keeping our things at our fingertips at all time
is fully realizable through Ai-Fi.net. We have integrated Apple Homekit into Ai-Fi.net to
demonstrate this capability. This is also an extension of Ai-Fi's Application Transparency
explained previously.
Many incompatible homekits
Many different device to homekits protocols
pairing
Most remote control solutions involve the cloud, incurring wider attack surface and privacy concerns
Support for Hybrid Cloud
Migrating your IT assets into the cloud is an excellent option if your cloud services can be trusted.
Ai-Fi.net will help extend your security perimeter to also cover your outsourced cloud elements.
Armed with the DiD stash and the self-administered crypto wallet we are now able to ramp up our private
assets into the cloud anonymously. As long as the payments are met through your Ai-Fi Wallet, Ai-Fi.net accepts
any requests for extending user assets into the Ai-Fi cloud without knowing anything about the requesting users.
The possession of your cloud assets is completely anonymous.
Network/Federate with Public Addressability
Now you've built yourself a few fortresses, standing alone by themselves without the protection of any overlords in sight, casting a gloom over the wilderness of Internet. How do you associate with other friendly fortresses or even invite the public in if you are one of those brave souls?
Domain Address Types
Each branch declares a set of subnets that it hosts. A branch subnet is typically native and located within the branch. A branch subnet may also be declared as of type "transit" if the branch is used as a jump-off point onto the Internet for reaching the specified subnet. Those transit addresses allow the domain to direct private traffic along an optimized routing path in taking advantage of the superior network resources offered by Ai-Fi.net. An address not native or of transit type will be "split" off locally by the branch and routed to the destination directly through Internet without involving the Ai-Fi cloud.
Acceleration to Internet Servers
As a value-added service, a set of public Ai-Fi "transit" branches may be shared among all domains that want to gain accelerated
access to certain Internet sites or branches (such as www.salesforce.com and other SaaS sites).
DAP (Domain Access Proxy) Service
For those domains without public IP addresses or needing managed and protected access, Ai-Fi.net provides the DAP service through
which public facing addresses are offered to represent internal elements of domains. Public Internet users may reach internal domain
resources through them. This is also how "Home Server" for a decentralized federation can be constructed.
Security Considerations
By adopting Ai-Fi.net domain security with the Access Points functioning as firewalls, all accesses in and out of the domain are
authenticated and closely managed by means of the rules and policies defined for the specific domain. However, security is never
absolute. Identify what you want to protect and fortify the domain carefully against those identified risks.
 Steps or Less
Steps or Less




